End-to-End Support
Full guidance from initial assessment to post-launch maintenance.
 What We Do
What We DoWe perform comprehensive security assessments to uncover vulnerabilities, protect critical systems, and ensure compliance with industry security standards.
Connect With UsScan applications and systems to identify security weaknesses and misconfigurations. Early detection helps prevent potential cyber threats and system compromises.
Simulate real-world cyberattacks to uncover hidden vulnerabilities in applications and infrastructure. This provides insights into how attackers might exploit security gaps.
Evaluate web and mobile applications for common vulnerabilities such as injection attacks and authentication flaws. This ensures secure software development practices.
Validate access control mechanisms to ensure only authorized users can access sensitive resources. Proper authentication protects systems from unauthorized access.
Assess how sensitive data is stored, transmitted, and encrypted across systems. This ensures compliance with security standards and data protection best practices.
Verify systems meet regulatory and industry security requirements. Compliance testing helps organizations maintain trust and avoid regulatory risks.
Evaluate API endpoints for potential security vulnerabilities and access control weaknesses. Securing APIs is critical for protecting modern application architectures.
Implement monitoring systems to detect suspicious activity and emerging threats. Continuous security evaluation helps maintain a strong security posture.
 Our Testing Framework
Our Testing Framework  STEP 1 – SECURITY RISK ASSESSMENT
STEP 1 – SECURITY RISK ASSESSMENT We conduct a comprehensive evaluation of your application architecture, infrastructure, and data flows to identify potential security vulnerabilities and risk exposure.

 STEP 2 – SECURITY TEST STRATEGY & PLANNING
STEP 2 – SECURITY TEST STRATEGY & PLANNING Based on the risk assessment, we develop structured testing strategies to evaluate authentication mechanisms, access control, and data protection measures.

 STEP 3 – VULNERABILITY SCANNING & PENETRATION TESTING
STEP 3 – VULNERABILITY SCANNING & PENETRATION TESTING Our team performs vulnerability scanning and controlled penetration testing to simulate real-world attack scenarios and uncover hidden security flaws.

 STEP 4 – RISK ANALYSIS & REMEDIATION GUIDANCE
STEP 4 – RISK ANALYSIS & REMEDIATION GUIDANCE After identifying vulnerabilities, we evaluate their impact and provide actionable remediation strategies to enhance system protection and reduce security risks.

 STEP 5 – CONTINUOUS SECURITY MONITORING
STEP 5 – CONTINUOUS SECURITY MONITORING We establish monitoring frameworks to continuously track system vulnerabilities, detect threats, and maintain a strong security posture as systems evolve.

Experienced engineers with proven success in Software Testing
Save time and money with streamlined AI Integration.
We leverage latest technologies and industry best practices.
 Why Trust Ishvara Tech Consulting ?
Why Trust Ishvara Tech Consulting ?At Ishvara Tech Consulting LLP, we don’t just build software — we build intelligent digital ecosystems that drive measurable business impact. As an AI-first development company, we combine deep technical expertise with strategic thinking to deliver solutions that are scalable, secure, and future-ready.
Our team of handpicked global professionals brings years of experience across AI/ML, SaaS, cloud, and full-stack engineering. We work as an extension of your organization, aligning technology with your business vision to create long-term value, not just short-term delivery.
Your growth is our mission. Your success is our benchmark.
 OUR INDUSTRIES
OUR INDUSTRIES

AI-driven tools to boost donor engagement, transparency, and measurable impact.


Personalized AI experiences that increase conversions and strengthen customer loyalty.


Scalable AI and cloud solutions designed for efficient and high-performance operations.


AI-enabled automation to improve production efficiency and reduce operational downtime.


AI-driven insights and smart systems to accelerate sales and optimize property management.
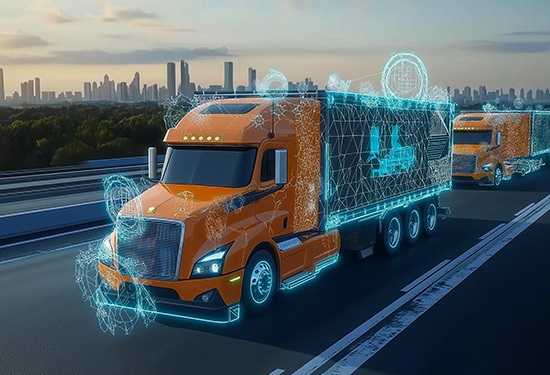

Intelligent routing and real-time analytics to improve efficiency, safety, and fleet performance.


AI-powered learning platforms that enhance engagement and deliver better student outcomes.


Smart, data-driven systems that improve decisions, patient care, and operational efficiency.

Security testing identifies vulnerabilities and ensures applications are protected from cyber threats.
It prevents data breaches, protects sensitive information, and ensures regulatory compliance.
We offer vulnerability assessments, penetration testing, authentication testing, and compliance validation.
Some security scans can be automated, but manual assessments are also required for deeper validation.
Security testing should be performed regularly, especially before product releases and after major system changes.
